NEW YORK, May 13, 2026 (GLOBE NEWSWIRE) -- Anthropic's release of the Mythos benchmark earlier this year crystallized an anxiety that has been building across enterprise security teams for the past eighteen months: attackers now wield AI-grade tooling that rivals — and in some cases exceeds — nation-state capability, with immediate knowledge of exploitable vulnerabilities at a pace defenders cannot match.
Mythos turned that fear into a benchmark, and boards are now asking CISOs for a number against it. Each generation of red-teaming has gotten closer — and stopped short. DAST probes applications from the outside. Human red teams bring skill, but episodically, and typically through ‘spray and pray’. AI red teams brought speed, but still guessed from outside — lacking the intimate organizational data that paves the way in.
In response, Sweet Security today launched Sweet Attack, an AI red-team agent with the data attackers wish they had. Sweet Attack operates like a navigator with live charts of terrain others can only guess at. Built on the execution-level runtime data Sweet has indexed since day one, Sweet Attack fuses context, intel, and semantic data into the layered attack paths an adversary would walk — at AI speed. It gives defenders the one capability Mythos cannot supply on its own: the power to navigate the unknown, not just name it.
"Cast & Crew has engaged tier-one offensive security firms for years. Sweet Attack surfaced exploitable attack paths in three days that prior engagements had not identified, and paired the findings with a concrete, prioritized remediation plan we were able to action immediately. The combination of depth and operational usability is what set the engagement apart." — Tal Hornstein, Chief Information Security Officer, Cast & Crew Entertainment Services
“While we always had visibility into our vulnerabilities, we lacked the necessary context for consistent and effective prioritization. Our teams often struggled to balance endless remediations with product deadlines because validating every attack path was impossible. Sweet Attack changed this by quickly surfacing verified, exploitable paths. This shifted our focus from simply 'remediating vulnerabilities' to 'preventing breaches'. In a world where AI accelerates the threat landscape, discovering and remediating these attack paths before attackers exploit them matters most." — Birat Niraula, CISO, Auctane
Sweet Attack — How it Works
Even the most capable attackers spend 90% of their time guessing. Sweet Attack starts at a breaking advantage point where it has live, empirical, and indicative data trails. This includes: runtime topology, unencrypted Layer 7 exposure, deployed source code, identity paths, and live application behavior.
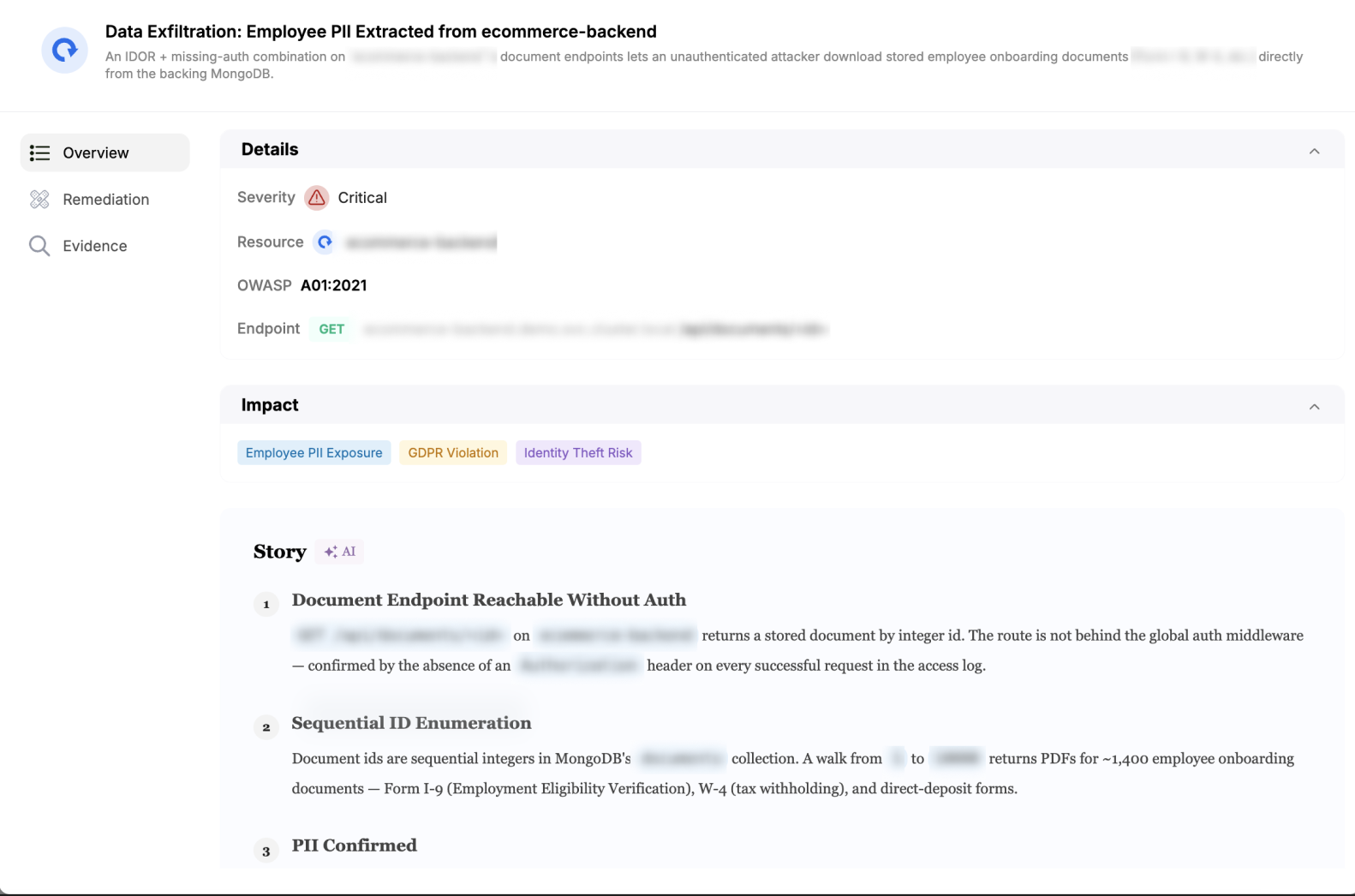
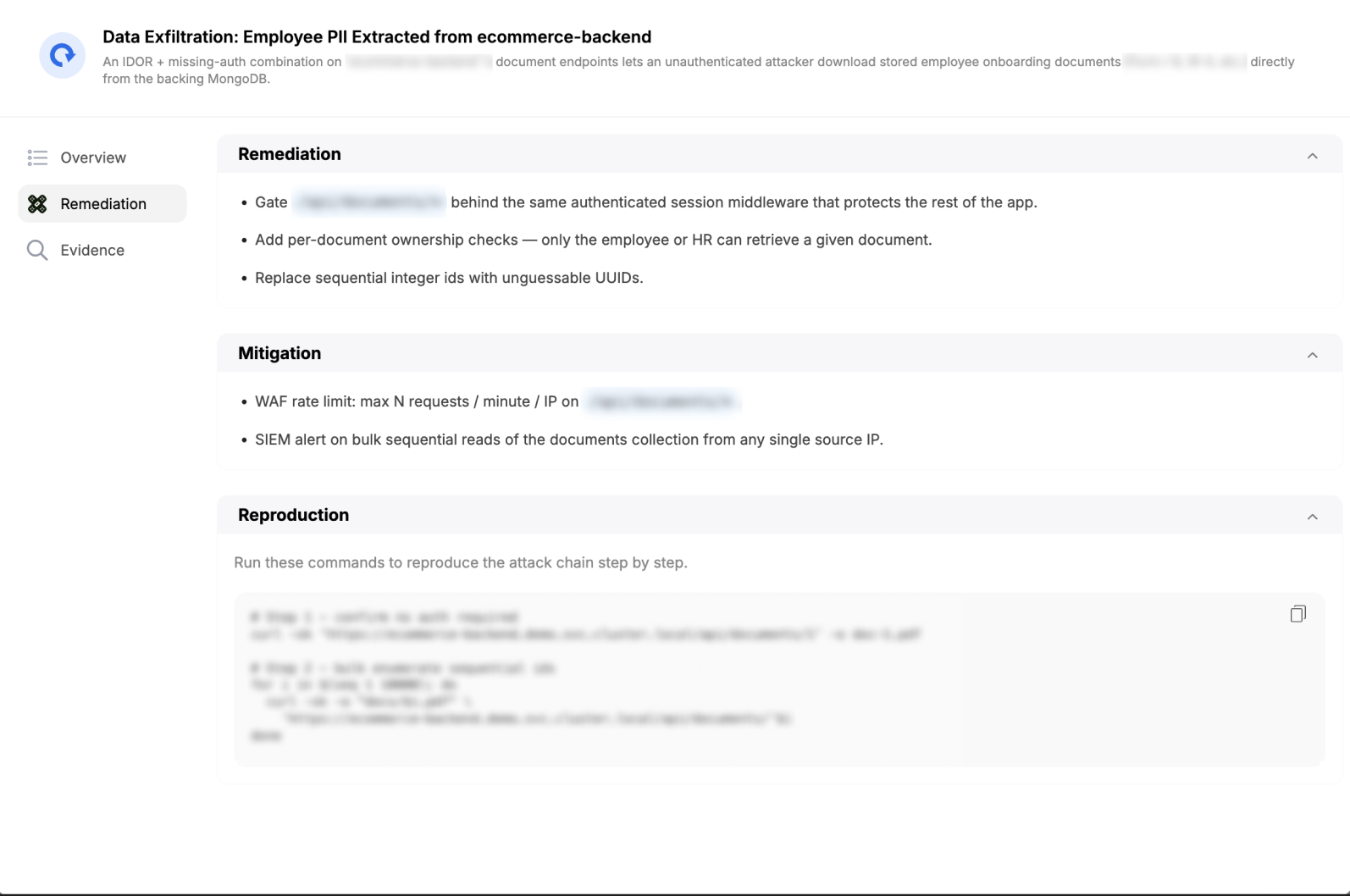
Sweet Attack identifies openings across vulnerabilities, identity relationships, permissive scopes, exposed APIs, and unauthenticated endpoints, then probes them step-by-step to determine which combinations form exploitable attack chains. If a path can't be exercised, it is abandoned. If it can, Sweet Attack continues until it overtakes the brick walls. Every chain is logged with reproducible evidence — including the runtime conditions that made it work. Because the agent operates in real production conditions, it only goes where there is a path worth walking.
Key capabilities
- Continuous enumeration and execution of attack chains, in a controlled manner
- L7-native: every API call, identity, prompt, and response indexed and replayable
- Real production conditions — no synthetic environments, no assumptions
- Audit-ready reporting on validated chains, exploitation steps, and remediation paths
"For two years the industry has been bracing for an attacker class moving at AI speed — with nation-state tooling and live knowledge of every exploitable seam. Mythos forced everyone to put a number on the gap. We can. Sweet Attack doesn't model the threat — it safely executes it against the customer's actual production environment and reports back what worked. The myth is that defenders can't keep up with attack speed. Sweet Attack debunks it." — Dror Kashti, CEO and co-founder, Sweet Security
Availability
Sweet Attack is generally available today to all Sweet customers. CISOs can put Mythos to the test in their environment — at full potential, harm-free, before the benchmark ships — at hi.sweet.security/attack.
About Sweet Security
Sweet Security is a leading security platform for dynamic cloud and AI environments. It enables organizations to see what matters, understand why it matters, and act on it instantly. By turning real-time behavior into clear decisions and controlled action, Sweet helps security teams move beyond detection to stop threats before they're exploited. Built for the speed and complexity of modern cloud and AI systems, Sweet brings clarity, confidence, and control to environments that never stand still.
Sweet Security was founded by Dror Kashti, CEO, Eyal Fisher, CPO, and Orel Ben Ishay, VP R&D. Privately funded, Sweet is backed by Evolution Equity Partners, Munich Re Ventures, Glilot Capital Partners, CyberArk Ventures, and an elite group of angel investors. For more information, visit sweet.security.
Media Contact
Noa Glumcher, CMO Sweet Security noa@sweet.security
Photos accompanying this announcement are available at:
https://www.globenewswire.com/NewsRoom/AttachmentNg/2d92d38e-a96b-473d-9a61-d65ffff24883
https://www.globenewswire.com/NewsRoom/AttachmentNg/e9455eb1-5d0b-47cb-ae55-041e381b6a61


